Most vulnerabilities are not the end of your world.
It's common to get large lists of what's wrong from a security organization, a cybersecurity insurance company, or a consultant. But these scans often don't tell the complete story.
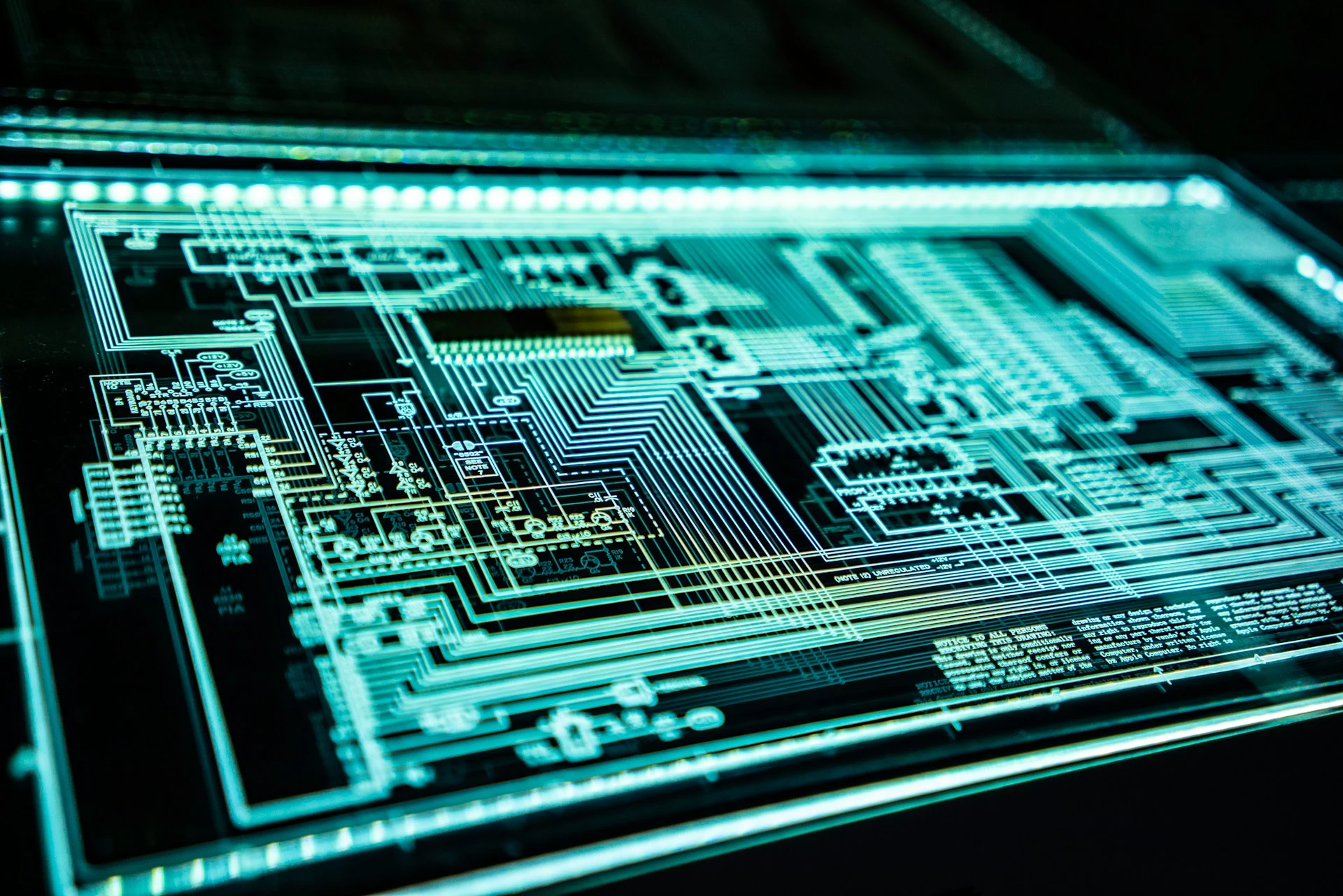
Software is constantly evolving. As a result, there’s a continuous battle: the “good” people making the infrastructure, hardware, and software, and the “bad” people trying to access the systems they shouldn’t have access to. There’s never a time when you can expect to find zero vulnerabilities.
Therefore, knowing which vulnerabilities to focus on is key.
Vulnerability scans can highlight potential vulnerabilities in your organization.
But not everything on the list needs to be an issue. That's because the scanning tools often are inclusive — not considering your specific use cases and environments.
Finding vulnerabilities should be proactive and is expected in any organization. And while everyone would love a vulnerability scan stating you're a hundred percent secure, that rarely happens, the scans are often subject to mistakes and need further clarification. That means you don’t have to fix every problem.
And if a scan lists a problem, it doesn’t mean it’s as big as it may seem on the list. More factors go into determining whether a vulnerability is worth remediating.
Detecting a vulnerability is only half the battle. You will almost always find them.
The key is understanding the environment and correcting the vulnerabilities most likely to harm the organization, knowing that requires knowledge of how an exploit or vulnerability could affect the individual organization.
The other half is remediating or removing the vulnerability. Either through a mitigating measure, meaning stopping it from becoming a problem, or removing the potential risk of someone accessing the vulnerability. Or through a patch that removes the vulnerability completely.
Figuratively speaking, it's sometimes a matter of taking all your money out of your safe, so it's no longer a problem if someone breaks into the safe.
It’s important to know the threats to the organization, the level of damage they could cause, and their remediation status.
As an MSP, Amoeba Networks provides these services for companies.
But in this communication, knowing what's happening is more critical than knowing how. Every vulnerability comes with a lot of technical information.
Redefining and explaining the information about every vulnerability would not be productive. As two examples, Log4j is a recent world-ending vulnerability discovered in the popular open-source software. And a couple of weeks ago, Janet Jackson's Rhythm Nation music video from 1989 was declared a security vulnerability because certain older hard drives would crash if it played around them.
Even though both are vulnerabilities, the Log4j vulnerability is most likely a more relevant threat than Janet Jackson's music, impacting older and often obsolete hard drives.
CVVS scores can help communicate vulnerabilities.
But because the scoring system assigns a threat level to specific vulnerabilities, that doesn't necessarily mean it applies to your environment. Many organizations also get caught in the vulnerability scan report, saying they need a report showing what they will do to fix this report.
Over Communicating technical details exacerbates the business problem rather than remediates it — and creates unnecessary overhead. Ensure that communication and reporting don’t become the focus of your vulnerability management process. The reason vulnerability management exists is not to have meetings and create reports.
After all, they’re tools to simplify system communication.
Onboarding and offboarding, especially in larger organizations, constantly change the environment, as does the technological evolution of any business.
Working with an incomplete list of assets will always yield incomplete results when managing vulnerabilities. But what should your list contain?
It’s more than a list of computers and their respective owners.
- Servers
- Mobile devices
- SaaS accounts
- Software in use
- Operating systems
- Third-party devices
- Networking equipment
- Authentication systems
You can’t correct a problem if you don’t see the entire picture.
Therefore, listing all assets is key to assessing your true state of vulnerabilities.
Correcting vulnerability problems is an endless and repetitive process.
Working off a to-do list isn't feasible. And as always, with manual, repetitive tasks, you can expect errors sooner or later when working at scale.
Automation is not only recommended in vulnerability management; it’s a necessity.
- Security alerts
- Log aggregation
- Vulnerability scans
- Operating system and software patching
Automating these critical areas allows you to spend energy assessing and remediating the vulnerabilities that matter.
There's always a new threat on the horizon.
No individual action or plan can completely secure an organization from vulnerabilities. So instead of trying to remediate every issue, the best approach to vulnerability management is proactive and selective.
And when a patch or solution isn’t available, taking steps to mitigate risks can make the difference between an incident and a follow-up item on a to-do list. But staying up to date with this information is a huge task, and mitigating threats is a full-time job. That's why organizations should have someone, either a consultant, an MSP, or a security team member, to help.
Amoeba Networks can take full responsibility for your vulnerability management to ensure your business stays secure against the growing number of cybersecurity threats.